JWT = 양파

자꾸 공부하면 공부할수록 뭔 양파마냥 알아야 할게 자꾸 나온다.. 미쳐버릴지경
어떻게 구현할거냐면
- 사용자 검증 UserDetailsService
- 비밀번호 비교 PasswordEncoder
- Authentication 객체 생성
- JWT 발급
- 클라이언트에 토큰 전달
- Filter 구현
순서대로 작성할 예정이다.
작성 순서
@Service
@RequiredArgsConstructor
@Slf4j
public class AuthService {
private final AuthenticateHandler authenticateHandler;
private final JwtProvider jwtProvider;
private final UserDetailsServiceImpl userDetailsServiceImpl;
public TokenDTO login(LoginRequestDTO request) {
PasswordEncoder passwordEncoder = new BCryptPasswordEncoder();
/*
* (1) 사용자 검증(UserDetailsService)
* */
UserDetailsDTO userDetails = (UserDetailsDTO) userDetailsServiceImpl.loadUserByUsername(request.getUserId());
/*
* (2) 비밀번호 비교(PasswordEncoder)
* */
if (!passwordEncoder.matches(request.getPassword(), userDetails.getPassword())) {
throw new BadCredentialsException("비밀번호가 일치하지 않아!(T_T)");
}
/*
* (3) Authentication 객체 생성
* */
Authentication authentication = authenticateHandler.authenticate(request);
// (4) JWT 발급
String accessToken = jwtProvider.createAccessToken(authentication);
// (5) 클라이언트에 토큰 전달
return new TokenDTO(accessToken);
}
}1. 사용자 검증
DB에서 유저 정보를 조회하고 UserDetails 객체를 만든다. ex) 이 username을 가진 유저가 있나요? → UserDetailsImpl 만들어서 스프링 시큐리티에 제공한다.
로그인은 2단계로 이루어지는데, 첫번째는 사용자 검증(Authentication 준비), 두번째는 비밀번호 검증(Authentication 완료) 단계이다.
사용자 검증은 "너가 누군지", 즉 이 userId를 가진 사람이 실제로 존재하는지, 그리고 DB에 등록된 사용자인지 검증을 한다.
비밀번호 검증은 "진짜 너가 맞는지"를 확인하는 단계이다.
이 2단계가 섞이면 위험하기 때문에 시큐리티는 일부러 나눠놨다.
| 역할 | 책임 |
| UserDetailsService | 이 사용자가 존재하는지 |
| UserDetails | 이 사용자의 정보는 무엇인지 |
| AuthenticationProvider | 비밀번호가 맞는지 |
| SecurityContext | 로그인 완료 후 상태 저장 |
그리하여 사용자 검증 단계에선
- ❌ 로그인 성공 처리 안 함
- ❌ 세션/JWT 안 만듦
- ⭕ “이 사람이 누구인지 설명서만 전달”
를 처리하면 된다.
2. 비밀번호 비교
입력한 비밀번호를 암호화했을 때 DB의 암호값고 동일한지 확인한다.
사실 이 과정은 Authentication 과정이 있으면 굳이 필요하진 않다고 하는데.. 그냥 공부차 작성한다.
PasswordEncoder passwordEncoder = new BCryptPasswordEncoder();
if (!passwordEncoder.matches(request.getPassword(), userDetails.getPassword())) {
throw new BadCredentialsException("비밀번호가 일치하지 않아!");
}(1) PasswordEncoder
비밀번호를 안전하게 암호화하고, 입력된 비밀번호와 저장된 암호회된 비밀번호를 비교하는 인터페이스
public interface PasswordEncoder {
// 비밀번호를 단방향 암호화
String encode(CharSequence rawPassword);
// 암호화되지 않은 비밀번호(raw-)와 암호화된 비밀번호(encoded-)가 일치하는지 비교
boolean matches(CharSequence rawPassword, String encodedPassword);
// 암호화된 비밀번호를 다시 암호화하고자 할 경우 true를 return하게 설정
default boolean upgradeEncoding(String encodedPassword) { return false; };
}이런식으로 구성되어 있고, PasswordEncoder 구현 클래스는 4개가 있다.
- BcryptPasswordEncoder : BCrypt 해시 함수를 사용하여 비밀번호를 암호화
- Argon2PasswordEncoder: Argon2 해시 함수를 사용해 비밀번호를 암호화
- Pbkdf2PasswordEncoder : PBKDF2 해시 함수를 사용하여 비밀번호를 암호화
- SCryptPasswordEncoder : SCrypt 해시 함수를 사용해서 비밀번호 암호화
여기서 BCryptPasswordEncoder를 이용했다. 단순한 해싱이 아닌 솔트(Salt)라는 렌덤 데이터를 추가하여 보안성을 높인다. 동일한 비밀번호도 암호화에 따라 결과값이 달라지기 때문에 원래 비밀번호를 알아내기 매우 어렵다.
(2) matches(평문, 암호문)
저장된 암호문(userDetails.getPassword())에서 사용됬던 솔트(Salt)값을 추출한다. 추출된 솔트와 입력받은 평문 비밀번호를 결합하여 다시 해싱한 후, 그 결과가 저장된 암호문과 같은지 확인한다.
(3) BadCredentialsException
Spring Security에서 제공하는 표준 예외로, 자격증명(id/pw)이 유효하지 않을 때 발생한다. 사용자의 id에 해당하는 패스워드가 일치하지 않을 때, 사용자의 아이디가 전달되지 않을 때 등등!
이 예외가 발생하면 보통 Spring Security의 인증 필터가 이를 가로채서 로그인 실패 페이지로 리다이렉트하거나, 401 unauthorized 에러 응답을 보내게 된다
3. Authentication 객체 생성
private final AuthenticateHandler authenticateHandler;
Authentication authentication = authenticateHandler.authenticate(request);Authentication 객체를 생성하는 과정은 "이 사용자가 정말 우리 회원이 맞는지 시스템적으로 최종 승인 도장을 찍는 과정"이라고 생각하면 된다.
Authentication 객체란?
Spring Security에서 Authentication은 현재 로그인한 사용자의 신원 보증서이다.
- Principal: 사용자의 아이디 혹은 사용자 객체
- Credentials: 비밀번호(인증에 사용된 증거)
- Authorities: 사용자가 가진 권한
- Authenticated: 인증 여부(T/F)
(1) AuthenticationManager 수동 생성
@Bean
public AuthenticationManager authenticationManager() throws Exception {
return authenticationConfiguration.getAuthenticationManager();
}AuthenticationManager은 "인증 센터의 총책임자"이다. 말 그대로 인증(Authentication)을 처리하는 관리자인데, 사용자가 로그인을 시도하면 그 정보가 맞는지 확인한다.
예전 Spring Security는 WebSecurityConfigurerAdapter이라는걸 상속받으면 자동으로 AuthenticationManager을 생성해줬는데, 요즘은(5.7버전 이상)은 컴포넌트 기반 설정으로 바뀌면서 보안상의 이유로 자동 Bean 생성은 안해주고 개발자가 명시해야 한다고 한다.............
그래서 Bean으로 등록을 해줬다.
- AuthenticationConfiguration : 스프링이 내부적으로 만들어둔 인증 설정 정보
- .getAuthenticationManager() : 이미 설정된 정보(UserDetailsService, PasswordEncoder 등)를 바탕으로 완성한 "총책임자(Manager)"를 꺼내오는 과정
(2) AuthenticationHandler
@Service
@Slf4j
@RequiredArgsConstructor
public class AuthenticateHandler {
private final AuthenticationManager authenticationManager;
public Authentication authenticate (LoginRequestDTO request) {
try {
return authenticationManager.authenticate(
new UsernamePasswordAuthenticationToken(
request.getUserId(),
request.getPassword()
)
);
} catch (BadCredentialsException e) {
log.warn("인증 실패 - 사용자: {} (잘못된 비밀번호)", request.getUserId());
throw e;
} catch (UsernameNotFoundException e) {
log.warn("인증 실패 - 사용자: {} (존재하지 않는 계정)", request.getUserId());
throw e;
} catch (Exception e) {
log.error("인증 중 오류 발생 - 사용자: {}", request.getUserId(), e);
throw e;
}
} // authenticate
}1️⃣ UsernamePasswordAuthenticationToken() 생성
사용자가 보낸 아이디와 비밀번호를 담은 인증 요청용 토큰을 먼저 만든다.
이때는 아직 검증되지 않았기 때문에 setAuthenticated(false) 상태인 일종의 로그인 신청서와같다.
2️⃣ AuthenticationManager.authenticate() 호출
이 "신청서"를 AuthenticationManager에게 전달한다.
관리자는 내부적으로 등록된 AuthenticationProvider들을 찾아 이 아이디와 비밀번호가 진짜 맞는지 확인한다.
3️⃣ 최종 Authentication 객체 반환(인증 완료)
내부 검증(비밀번호 비교 등)이 성공하면, 사용자의 권한(Roles)과 상세 정보가 포함된 새로운 Authentication 객체를 반환한다.
이 객체는 setAuthenticatted(true)상태이며, 이제 시스템 어디서든 "이 사람은 믿을 수 있는 사용자다" 라고 인정받게 된다.
4. JWT 발급
@Component
public class JwtProvider {
private Long ACCESS_TOKEN;
private Key secretKey = Keys.secretKeyFor(SignatureAlgorithm.HS256);
public String createAccessToken (Authentication authentication) {
UserDetailsDTO principal = (UserDetailsDTO) authentication.getPrincipal();
String userId = principal.getUserId();
List<String> roles = principal.getAuthorities().stream().map(GrantedAuthority::getAuthority).toList();
Date now = new Date();
Date expiry = new Date(now.getTime() + ACCESS_TOKEN);
return Jwts.builder()
.setSubject(userId)
.claim("role", roles)
.setIssuedAt(now)
.setExpiration(expiry)
.signWith(secretKey, SignatureAlgorithm.HS256)
.compact();
}
}createAccessToken : 새로운 토큰을 생성하는 메소드
- ACCESS_TOKEN : application.yml 혹은 properties에서 설정된 만료시간 값을 가져온다
- secretKey : 서명(Signature)을 위한 키. HS256알고리즘에 적합한 안전 키를 자동으로 생성.
- Keys.secretKeyFor는 서버가 재시작될 때 마다 새로운 키를 생성한다.
(1) 사용자 정보 추출(Payload 준비)
- authentication.getPrincipal() : 앞선 단계에서 생성했던 인증 객체에서 사용자 상세정보를 꺼냄(UserDetailsDTO). 토큰 내부에 저장할 사용자 ID와 권한목록을 준비
(2) JWT 토큰 생성
- setSubject : 토큰의 식별자. 보통 사용자 고유 아이디를 넣음
- claim("role", roles) : 표준 필드 외에 개발자가 추가하고 싶은 정보를 넣음
- setIssuedAt(now) : 토큰 발행 시간
- setExpiration(expiry) : 토큰 만료 시간
- signWith(secretKey, SignatureAlgorithm.HS256) : 암호화 서명. 준비한 secretKey와 HS256알고리즘을 사용해 토큰이 위조되지 않음을 증명하는 서명. 가장 중요한 보안 단계
- compact() : 모든 설정을 마치고 최종적으로 header.payload.signature 형태의 긴 문자열을 반환
5. 클라이언트에 토큰 전달
return new TokenDTO(accessToken);6. Filter 구현
만났던 오류 사항
1. java.lang.StackOverflowError
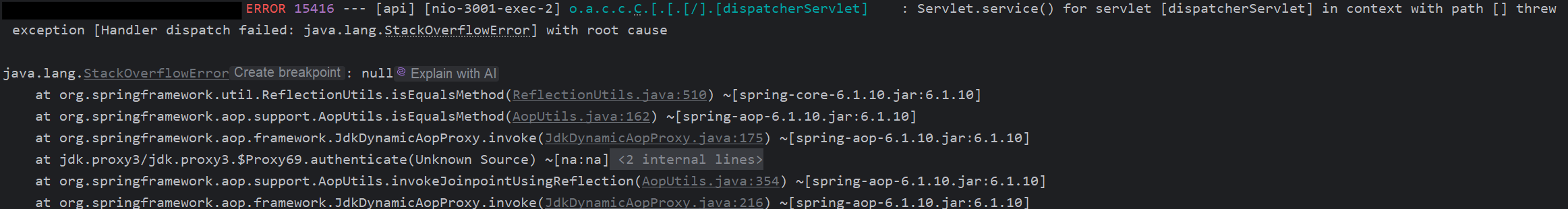
메소드 호출이 너무 깊어져서 스택 메모리가 가득 찼을 때 발생하는 에러이다.
at org.springframework.aop.framework.JdkDynamicAopProxy.invoke(JdkDynamicAopProxy.java:216) ~[spring-aop-6.1.10.jar:6.1.10]
at jdk.proxy3/jdk.proxy3.$Proxy69.authenticate(Unknown Source) ~[na:na]
at java.base/jdk.internal.reflect.DirectMethodHandleAccessor.invoke(DirectMethodHandleAccessor.java:103) ~[na:na]
at java.base/java.lang.reflect.Method.invoke(Method.java:580) ~[na:na]이게 무한반복되는걸 확인했다.
AuthenticateHandler와 같이 Authentication과 관련된 과정에서 무언가가 무한반복해서 호출하는거라는건 어림짐작 할 수 있었다.
Spring AOP 프록시와 관련된 재귀문제라고 한다.
GPT의 추가설명 👽
1. 프록시 객체 ($Proxy69)
- $Proxy69.authenticate는 @Service나 @Component와 같은 Spring Bean에 트랜잭션(@Transactional)이나 보안(AOP)과 같은 부가 기능이 적용될 때, **Spring이 원본 객체 대신 생성하여 주입하는 대리 객체(Proxy)**입니다.
- 당신의 코드에서는 AuthenticationManager 빈이 이 프록시 객체로 주입된 것입니다.
2. 프록시의 invoke
- JdkDynamicAopProxy.invoke는 이 프록시 객체의 메서드(여기서는 authenticate)가 호출될 때 항상 먼저 실행되는 Spring AOP의 핵심 로직입니다. 이 로직은 부가 기능을 처리한 후 원본 객체의 메서드를 호출합니다.
3. 무한 재귀 (Stack Overflow)
StackOverflowError가 발생했다는 것은 다음과 같은 순환 호출 구조가 발생했다는 의미입니다.
- 시작: AuthService (또는 외부) $\rightarrow$ 프록시 AuthenticationManager의 authenticate() 호출
- 프록시: JdkDynamicAopProxy.invoke 실행
- 문제: invoke 로직이 **원본 AuthenticationManager**를 호출하는 대신, 어떤 경로를 통해 다시 1번 단계로 돌아가 프록시 객체의 authenticate()를 재호출합니다.
이 무한 루프의 원인은 앞선 답변에서 설명드렸듯이, AuthenticationManager 빈을 정의하는 과정(SecurityConfig)과 이를 사용하는 커스텀 인증 로직(AuthenticateHandler 또는 AuthService) 간의 의존성 주입(DI) 충돌이나 설정의 중복 때문입니다.
결론 :
오류 발생 지점은 AuthenticationManager의 authenticate()의 호출 과정
원인은 Spring Security의 설정과 커스텀 로직 간의 순환 참조(Circular Dependency)
- DB에서 직접 사용자정보 조회(getUserDetails)
- 비밀번호를 직접 비교(passwordEncoder.matches)
- authenticatHandler.authenticate(request)를 통해 다시 인증 시도
- 즉, 로그인 로직 안에서 Spring Security의 인증을 '수동' + '자동'으로 동시에 돌리면서 인증 과정이 자기 자신을 계속 호출하여 stackOverflow 발생 (길어져서 접은글 작성)
authenticateHandler.authenticate() 안에서 무슨 일이 일어났나?
AuthenticateHandler는 내부에서 보통 이런 걸 하고 있어:
즉,👉 Spring Security의 표준 인증 프로세스(AuthenticationManager) 를 다시 호출함
Spring Security는 이 인증을 어떻게 처리하나?
Spring Security는 인증을 시작하면:
- AuthenticationManager 실행
- AuthenticationProvider 호출
- UserDetailsService.loadUserByUsername() 호출
- (AOP / Filter / Security 설정에 따라)
- 커스텀 로그인 로직(AuthService.login())을 다시 타게 됨
그래서 무슨 일이 벌어졌나? (무한 루프)
AuthService.login()
└ authenticateHandler.authenticate()
└ AuthenticationManager.authenticate()
└ Spring Security 인증 시작
└ AuthService.login() 다시 호출
└ authenticateHandler.authenticate()
└ AuthenticationManager.authenticate()
└ ...🎢 끝없는 회전목마
➡️ StackOverflowError 발생
문제를 해결하기 위해선 AuthenticationManager을 사용하지 않고, 이미 코드에선 직접 비밀번호 검증을 하고 있기때문에 인증 객체를 수동으로 생성하라고 하는데...
public class AuthService {
private final JdbcTemplate jdbcTemplate;
private final AuthenticateHandler authenticateHandler;
private final JwtProvider jwtProvider;
public TokenDTO login(LoginRequestDTO request) {
PasswordEncoder passwordEncoder = new BCryptPasswordEncoder();
UserDetailsImpl userDetails = getUserDetails(request);
if (!passwordEncoder.matches(request.getPassword(), userDetails.getPassword())) {
// 비밀번호가 일치하지 않다면
throw new BadCredentialsException("비밀번호가 일치하지 않아!(T_T)");
}
Authentication authentication = authenticateHandler.authenticate(request);
String accessToken = jwtProvider.createAccessToken(authentication);
return new TokenDTO(accessToken);
}근데 난 공부중이므로 AuthenticationManager을 사용해보고 싶다.
1️⃣ UserDetailsService 구현 클래스 생성
@Service
@RequiredArgsConstructor
@Slf4j
public class UserDetailsServiceImpl implements UserDetailsService {
public final JdbcTemplate jdbcTemplate;
@Override
public UserDetails loadUserByUsername(String userId) {
String sql = "SELECT * FROM dalmuri.\"USER\" WHERE \"USER_ID\" = ?"; // 여기 에러는 무시 가능
UserDetailsImplDTO userImpl = new UserDetailsImplDTO();
try {
UserDTO user = jdbcTemplate.queryForObject(
sql,
new Object[]{userId},
(rs, rowNum) -> { // Mapper
UserDTO u = new UserDTO();
u.setUserCd(rs.getString("USER_CD"));
u.setUserId(rs.getString("USER_ID"));
u.setUserNm(rs.getString("USER_NM"));
u.setPassword(rs.getString("PASSWORD"));
u.setBgColor(rs.getString("BG_COLOR"));
u.setTextColor(rs.getString("TEXT_COLOR"));
u.setInsertDatetime(rs.getString("INSERT_DATETIME"));
return u;
}
);
if (user == null) {
throw new UsernameNotFoundException("사용자 정보 없음: " + userId);
}
userImpl.setUserCd(user.getUserCd());
userImpl.setUserId(user.getUserId());
userImpl.setUserNm(user.getUserNm());
userImpl.setPassword(user.getPassword());
userImpl.setBgColor(user.getBgColor());
userImpl.setTextColor(user.getTextColor());
userImpl.setInsertDatetime(user.getInsertDatetime());
return userImpl;
} catch (Exception e) {
e.printStackTrace();
throw new UsernameNotFoundException("사용자 정보 없음: " + userId);
}
}
}그리고 기존 AuthService.java에 있던 DB호출로직은 삭제
// private UserDetailsImpl getUserDetails (LoginRequestDTO request) {
// String sql = "SELECT * FROM dalmuri.\"USER\" WHERE \"USER_ID\" = ?"; // 여기 에러는 무시 가능
//
// User user = jdbcTemplate.queryForObject(
// sql,
// new Object[]{request.getUserId()},
// (rs, rowNum) -> { // Mapper
// User u = new User();
// u.setUserCd(rs.getString("USER_CD"));
// u.setUserId(rs.getString("USER_ID"));
// u.setUserNm(rs.getString("USER_NM"));
// u.setPassword(rs.getString("PASSWORD"));
// u.setBgColor(rs.getString("BG_COLOR"));
// u.setTextColor(rs.getString("TEXT_COLOR"));
// u.setInsertDatetime(rs.getString("INSERT_DATETIME"));
// return u;
// }
// );
//
// if (user == null) {
// throw new UsernameNotFoundException("사용자 정보 없음: " + request.getUserId());
// }
//
// return new UserDetailsImpl(user);
// }왜 삭제하냐면, AuthService에서 같이 생성했기 때문에 getUserDetails 메소드는 UserDetailsService 인터페이스를 상속받지 않는다(AuthService가 UserDetailsService를 상속받지 않음)
2️⃣ User을 UserDetails로 변환
@Getter
@Setter
@ToString
public class UserDetailsDTO implements UserDetails {
private String userCd;
private String userId;
private String userNm;
private String password;
private String bgColor;
private String textColor;
private String insertDatetime;
/*
* 1. Lombok 어노테이션을 사용해도 UserDetails에서 요구하는 인터페이스는 직접 작성해야 한다.
* */
private final String role = "ROLE_USER";
@Override
public String getUsername() {
return userId;
}
@Override
public String getPassword() {
return password;
}
@Override
public Collection<? extends GrantedAuthority> getAuthorities() {
// 고정 반환
return List.of(new SimpleGrantedAuthority(this.role));
}
/**
* 형식적인 요소들 : true로 고정
* */
@Override
public boolean isAccountNonExpired() {
return true;
}
@Override
public boolean isAccountNonLocked() {
return true;
}
@Override
public boolean isCredentialsNonExpired() {
return true;
}
@Override
public boolean isEnabled() {
return true;
}
}기존에 만들었던 UserDTO
@Getter
@Setter
@ToString
@NoArgsConstructor
@AllArgsConstructor
public class UserDTO {
private String userCd;
private String userId;
private String userNm;
private String password;
// 있으나 없으나
private String bgColor;
private String textColor;
private String insertDatetime;
}
3️⃣ AuthService.java 로직 수정
기존 로직
public class AuthService {
private final JdbcTemplate jdbcTemplate;
private final AuthenticateHandler authenticateHandler;
private final JwtProvider jwtProvider;
public TokenDTO login(LoginRequestDTO request) {
PasswordEncoder passwordEncoder = new BCryptPasswordEncoder();
UserDetailsImpl userDetails = getUserDetails(request);
if (!passwordEncoder.matches(request.getPassword(), userDetails.getPassword())) {
// 비밀번호가 일치하지 않다면
throw new BadCredentialsException("비밀번호가 일치하지 않아!(T_T)");
}
Authentication authentication = authenticateHandler.authenticate(request);
String accessToken = jwtProvider.createAccessToken(authentication);
return new TokenDTO(accessToken);
}
private UserDetailsImpl getUserDetails (LoginRequestDTO request) {
String sql = "SELECT * FROM dalmuri.\"USER\" WHERE \"USER_ID\" = ?"; // 여기 에러는 무시 가능
User user = jdbcTemplate.queryForObject(
sql,
new Object[]{request.getUserId()},
(rs, rowNum) -> { // Mapper
User u = new User();
u.setUserCd(rs.getString("USER_CD"));
u.setUserId(rs.getString("USER_ID"));
u.setUserNm(rs.getString("USER_NM"));
u.setPassword(rs.getString("PASSWORD"));
u.setBgColor(rs.getString("BG_COLOR"));
u.setTextColor(rs.getString("TEXT_COLOR"));
u.setInsertDatetime(rs.getString("INSERT_DATETIME"));
return u;
}
);
if (user == null) {
throw new UsernameNotFoundException("사용자 정보 없음: " + request.getUserId());
}
return new UserDetailsImpl(user);
}
}새로 고친 로직
@Service
@RequiredArgsConstructor
@Slf4j
public class AuthService {
private final AuthenticateHandler authenticateHandler;
private final JwtProvider jwtProvider;
private final UserDetailsServiceImpl userDetailsServiceImpl;
public TokenDTO login(LoginRequestDTO request) {
PasswordEncoder passwordEncoder = new BCryptPasswordEncoder();
UserDetailsDTO userDetails = (UserDetailsDTO) userDetailsServiceImpl.loadUserByUsername(request.getUserId());
if (!passwordEncoder.matches(request.getPassword(), userDetails.getPassword())) {
// 비밀번호가 일치하지 않다면
throw new BadCredentialsException("비밀번호가 일치하지 않아!(T_T)");
}
Authentication authentication = authenticateHandler.authenticate(request);
String accessToken = jwtProvider.createAccessToken(authentication);
return new TokenDTO(accessToken);
}
[참고 자료]
https://velog.io/@corgi/Spring-Security-PasswordEncoder%EB%9E%80-4kkyw8gi
[Spring Security] PasswordEncoder란?
Spring Security 5.3.3 버전에서 지원하는 PasswordEncoder에 대해 간략히 알아봅니다.
velog.io
https://coding-start.tistory.com/153
Spring boot - Spring Security(스프링 시큐리티) 란? 완전 해결!
오늘 포스팅할 내용은 Spring Security이다. 사실 필자는 머리가 나빠서 그런지 모르겠지만, 아무리 구글링을 통해 스프링 시큐리티를 검색해도 이렇다할 명쾌한 해답을 얻지 못했다. 대부분 이론적
coding-start.tistory.com
'Backend🖥️ > Java☕(Spring🍃)' 카테고리의 다른 글
| 람다식이란? (0) | 2026.01.29 |
|---|---|
| [Spring] JWT 이용해서 로그인 기능 만들기 - 필터 작성 (0) | 2026.01.07 |
| [Spring] JWT 이용해서 로그인 기능 만들기 - 사용자 검증 (1) | 2025.12.31 |
| [Spring] Spring Security 맛보기 (0) | 2025.12.11 |
| [Spring] Spring Security - application.yml로 URL권한을 동적으로 관리하기 (0) | 2025.10.20 |